Dan Lamothe reports: The U.S. military has conducted cyber attacks against the Islamic State for more than a year, and its record of success when those attacks are coordinated with elite Special Operations troops is such that the Pentagon is likely carry out similar operations with greater frequency, according to current and former U.S. defense officials.
The cyber offensive against ISIS, an acronym for the Islamic State, was a first and included the creation of a unit named Joint Task Force Ares. It focused on destroying or disrupting computer networks used by the militant group to recruit fighters and communicate inside the organization. Such offensive weapons are more commonly associated with U.S. intelligence agencies, but they were brought into the open in 2016 after then-Defense Secretary Ashton B. Carter pressured U.S. Cyber Command to become more involved in the campaign to defeat the Islamic State.
The move sparked a debate in the U.S. government over whether American allies would object to the U.S. military’s altering computer networks abroad, The Washington Post reported in May. Some intelligence officials argued that using such weapons in other countries could jeopardize the cooperation of international partners on which U.S. law enforcement and intelligence agencies depend.
But the cyber attacks were approved and launched anyway, and the campaign recently received the full-throated endorsement of Army Gen. Raymond A. “Tony” Thomas III, the head of U.S. Special Operations Command. [Continue reading…]
Category Archives: cyberwarfare
Following the developing Iranian cyberthreat
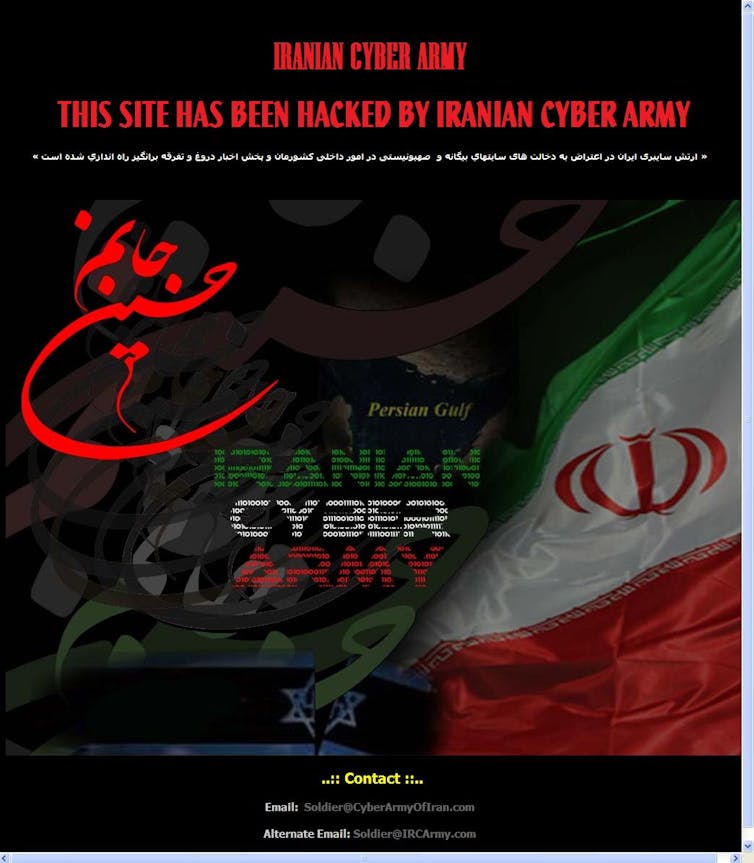
Zone-H, CC BY-NC-ND
By Dorothy Denning, Naval Postgraduate School
Iran is one of the leading cyberspace adversaries of the United States. It emerged as a cyberthreat a few years later than Russia and China and has so far demonstrated less skill. Nevertheless, it has conducted several highly damaging cyberattacks and become a major threat that will only get worse.
Like Russia and China, the history of Iran’s cyberspace operations begins with its hackers. But unlike these other countries, Iran openly encourages its hackers to launch cyberattacks against its enemies. The government not only recruits hackers into its cyberforces but supports their independent operations.
A guide to Russia’s high tech tool box for subverting U.S. democracy
Garrett M Graff writes: A dead dog in Moscow. A dead dissident in London. Twitter trolls run by the Kremlin’s Internet Research Agency. Denial of service attacks and ransomware deployed across Ukraine. News reports from the DC offices of Sputnik and RT. Spies hidden in the heart of Wall Street. The hacking of John Podesta’s creamy risotto recipe. And a century-old fabricated staple of anti-Semitic hate literature.
At first glance these disparate phenomena might seem only vaguely connected. Sure, they can all be traced back to Russia. But is there any method to their badness? The definitive answer, according to Russia experts inside and outside the US government, is most certainly yes. In fact, they are part of an increasingly digital intelligence playbook known as “active measures,” a wide-ranging set of techniques and strategies that Russian military and intelligence services deploy to influence the affairs of nations across the globe.
As the investigation into Russia’s influence on the 2016 election—and the Trump campaign’s potential participation in that effort—has intensified this summer, the Putin regime’s systematic effort to undermine and destabilize democracies has become the subject of urgent focus in the West. According to interviews with more than a dozen US and European intelligence officials and diplomats, Russian active measures represent perhaps the biggest challenge to the Western order since the fall of the Berlin Wall. The consensus: Vladimir Putin, playing a poor hand economically and demographically at home, is seeking to destabilize the multilateral institutions, partnerships, and Western democracies that have kept the peace during the past seven decades.
The coordinated and multifaceted Russia efforts in the 2016 election—from the attacks on the DNC and John Podesta’s email to a meeting between a Russian lawyer and Donald Trump Jr. that bears all the hallmarks of an intelligence mission—likely involved every major Russian intelligence service: the foreign intelligence service (known as the SVR) as well as the state security service (the FSB, the successor to the KGB), and the military intelligence (the GRU), both of which separately penetrated servers at the DNC.
Understanding just how extensive and coordinated Russia’s operations against the West are represents the first step in confronting—and defeating—Putin’s increased aggression, particularly as it becomes clear that the 2016 election interference was just a starting point. “If there has ever been a clarion call for vigilance and action against a threat to the very foundation of our democratic political system, this episode is it,” former director of national intelligence James Clapper said this spring. “I hope the American people recognize the severity of this threat and that we collectively counter it before it further erodes the fabric of our democracy.”
Indeed, Western intelligence leaders have warned throughout the spring that they expect Russia to use similar tricks in German parliamentary election this fall, as well as in the 2018 US congressional midterms and the 2020 presidential race. “Russia is not constrained by a rule of law or a sense of ethics—same with ISIS, same with China,” says Chris Donnelly, director of the UK-based Institute for Statecraft. “They’re trying to change the rules of the game, which they’ve seen us set in our favor.” [Continue reading…]
The hacking wars are going to get much worse
Adam Segal writes: Reports this month that the United Arab Emirates orchestrated the hacking of a Qatari news agency, helping to incite a crisis in the Middle East, are as unsurprising as they are unwelcome. For years, countries — in particular Russia — have used cyberattacks and the dissemination of disinformation through social media and news outlets to provoke protests, sway elections and undermine trust in institutions. It was only a matter of time before smaller states tried their hand at these tactics.
With few accepted rules of behavior in cyberspace, countries as big as China or as small as Bahrain can be expected to use these kinds of attacks. And they may eventually spill over into real-world military conflicts.
The hacking attacks in the Gulf seem to follow a typical pattern of going after the media and the email accounts of prominent individuals. According to American intelligence officials, in late May, hackers supported by the United Arab Emirates infiltrated Qatari government news and social media sites. The attackers planted quotations falsely attributed to Sheikh Tamim bin Hamad al-Thani, Qatar’s leader, praising Iran, Hamas and Israel. [Continue reading…]
Russia used Facebook to try to spy on Macron campaign
Reuters reports: Russian intelligence agents attempted to spy on President Emmanuel Macron’s election campaign earlier this year by creating phony Facebook personas, according to a U.S. Congressman and two other people briefed on the effort.
About two dozen Facebook accounts were created to conduct surveillance on Macron campaign officials and others close to the centrist former financier as he sought to defeat far-right nationalist Marine Le Pen and other opponents in the two-round election, the sources said. Macron won in a landslide in May.
Facebook said in April it had taken action against fake accounts that were spreading misinformation about the French election. But the effort to infiltrate the social networks of Macron officials has not previously been reported. [Continue reading…]
In cyberwarfare, everyone is a combatant
The Wall Street Journal reports: This is already a banner year for hacks, breaches and cyberwarfare, but the past week was exceptional.
South Carolina reported hackers attempted to access the state’s voter-registration system 150,000 times on Election Day last November—part of what former Homeland Security Secretary Jeh Johnson alleges is a 21-state attack perpetrated by Russia. And U.S. intelligence officials alleged that agents working for the United Arab Emirates planted false information in Qatari news outlets and social media, leading to sanctions and a rift with Qatar’s allies. Meanwhile, Lloyd’s of London declared that the takedown of a significant cloud service could lead to monetary damages on par with those of Hurricane Katrina.
Threats to the real world from the cyberworld are worse than ever, and the situation continues to deteriorate. A new kind of war is upon us, one characterized by coercion rather than the use of force, says former State Department official James Lewis, a cybersecurity specialist at the Center for Strategic and International Studies.
Businesses and individuals now are directly affected in ways that were impossible in the first Cold War. In another age, the threat of nuclear annihilation loomed over everyone’s heads, but the cloak-and-dagger doings of global powers remained distinct from the day-to-day operations of businesses. Now, they are hopelessly entangled. The often unfathomable priorities of terrorists, cybercriminals and state-affiliated hackers only make things worse.
The current climate of cyberattacks is “crazy,” says Christopher Ahlberg of Recorded Future, a private intelligence firm that specializes in cyberthreats. “It’s like a science-fiction book. If you told anybody 10 years ago about what’s going on now, they wouldn’t believe it.”
In the first Cold War, the U.S., China and the Soviet Union fought proxy wars rather than confront one another directly. In Cold War 2.0, we still have those—Syria and whatever is brewing in North Korea come to mind—but much of the proxy fighting now happens online.
The result is significant collateral damage for businesses that aren’t even a party to the conflicts, says Corey Thomas, chief executive of cybersecurity firm Rapid 7. Recent ransomware attacks that some analysts attribute to Russia might have been aimed at Ukraine but resulted in the shutdown of computer systems at businesses and governments around the world. Russia has denied involvement in these attacks. Botnets made of internet-connected devices, stitched together by an unknown hacker for unknown reasons, caused countless internet services and websites to become unavailable in October 2016. [Continue reading…]
Trump’s plan to work with Putin on cybersecurity makes no sense. Here’s why
Henry Farrell writes: During the Obama administration, the United States and China reached an agreement on how to deal with contentious issues in cybersecurity. Both the United States and China hack into each other’s systems on a regular basis. The agreement was not intended to stop this but to prevent it from getting out of control in ways that might damage bilateral arrangements. Thus, the agreement created a kind of hotline for communication and information sharing about potentially problematic behavior, as well as a continuing dialogue on cyber issues. It also ruled out efforts by state actors to steal intellectual property (the United States had persistently complained that Chinese state hackers stole U.S. companies’ secrets and passed them on to Chinese competitor firms). To the surprise of many in the United States, the agreement seems to have helped moderate Chinese efforts to steal commercial secrets, although there is disagreement over whether this was because China was shamed and wanted to preserve honor, or alternatively used the agreement to impose control over unruly hackers.
Either way, this deal worked — to the extent it did work — because both states had roughly convergent interests over a very limited set of issues. It did not involve the exchange of truly sensitive information — China does not trust the United States with details of its defenses against cyberattacks, and the United States does not trust China. Instead, the two sides have looked to manage their disagreement, rather than engage in deep and extensive cooperation.
That doesn’t appear to be what Trump wants
As Trump has described his discussions with Putin, both want something much more far-reaching than the deal that Obama reached with China. Instead of setting up dialogue, Trump wants to engage in true cooperation. He wants to set up a joint “unit” that would handle election security issues so as to prevent hacking. This unit would, furthermore, be “impenetrable.”
Critics in the United States have unsurprisingly interpreted this proposal as a transparent ploy by Trump to sideline accusations that Russian hackers helped him win the presidential election. However, even if Trump’s proposal is taken at face value, it doesn’t make much sense.
U.S. officials don’t trust the Russians
If the proposed cybersecurity unit were to work effectively, the United States would need to share extensive information with Russia on how U.S. officials defend elections against foreign tampering. The problem is, however, that information that is valuable for defending U.S. systems is, almost by definition, information that is valuable for attacking them, too. This is one reason U.S. officials have not previously proposed any far-reaching arrangement with Russia on cybersecurity. Providing such information would almost certainly give the Russians a map of vulnerabilities and insecurities in the system that they could then exploit for their own purposes.
It would not only provide the fox with a map of the henhouse, but give him the security code, the backdoor key, and a wheelbarrow to make off with the carcasses. [Continue reading…]
U.S. officials say Russian government hackers have penetrated energy and nuclear company business networks
The Washington Post reports: Russian government hackers were behind recent cyber-intrusions into the business systems of U.S. nuclear power and other energy companies in what appears to be an effort to assess their networks, according to U.S. government officials.
The U.S. officials said there is no evidence the hackers breached or disrupted the core systems controlling operations at the plants, so the public was not at risk. Rather, they said, the hackers broke into systems dealing with business and administrative tasks, such as personnel.
At the end of June, the FBI and the Department of Homeland Security sent a joint alert to the energy sector stating that “advanced, persistent threat actors” — a euphemism for sophisticated foreign hackers — were stealing network log-in and password information to gain a foothold in company networks. The agencies did not name Russia.
The campaign marks the first time Russian government hackers are known to have wormed their way into the networks of American nuclear power companies, several U.S. and industry officials said. And the penetration could be a sign that Russia is seeking to lay the groundwork for more damaging hacks. [Continue reading…]
Trump handed Putin a stunning victory
Molly K McKew writes: President Donald Trump needed to accomplish two things this week during his visits to Poland and the G-20 Summit in Hamburg. First, he needed to reassure America’s allies that he was committed to collective defense and the core set of values and principles that bind us together. Second, he needed to demonstrate that he understands that the greatest threat to that alliance, those values, and our security is the Kremlin.
Trump delivered neither of these. In very concrete terms, through speech and action, the president signaled a willingness to align the United States with Vladimir Putin’s worldview, and took steps to advance this realignment. He endorsed, nearly in its totality, the narrative the Russian leader has worked so meticulously to construct.
The readout of Trump’s lengthy meeting with Putin included several key points. First, the United States will “move on” from election hacking issues with no accountability or consequences for Russia; in fact, the U.S. will form a “framework” with Russia to cooperate on cybersecurity issues, evaluating weaknesses and assessing potential responses jointly. Second, the two presidents agreed not to meddle in “each other’s” domestic affairs—equating American activities to promote democracy with Russian aggression aimed at undermining it, in an incalculable PR victory for the Kremlin. Third, the announced, limited cease-fire in Syria will be a new basis for cooperation between the U.S. and Russia; Secretary of State Rex Tillerson went so far as to say that the Russian approach in Syria—yielding mass civilian casualties, catastrophic displacement, untold destruction and erased borders—may be “more right” than that of the United States.
Each of these points represents a significant victory for Putin. Each of them will weaken U.S. tools for defending its interests and security from the country that defines itself as America’s “primary adversary.” Trump has ceded the battle space—physical, virtual, moral—to the Kremlin. And the president is going to tell us this is a “win.” [Continue reading…]
Russians are suspects in nuclear site hackings, sources say
Bloomberg reports: Hackers working for a foreign government recently breached at least a dozen U.S. power plants, including the Wolf Creek nuclear facility in Kansas, according to current and former U.S. officials, sparking concerns the attackers were searching for vulnerabilities in the electrical grid.
The rivals could be positioning themselves to eventually disrupt the nation’s power supply, warned the officials, who noted that a general alert was distributed to utilities a week ago. Adding to those concerns, hackers recently infiltrated an unidentified company that makes control systems for equipment used in the power industry, an attack that officials believe may be related.
The chief suspect is Russia, according to three people familiar with the continuing effort to eject the hackers from the computer networks. One of those networks belongs to an aging nuclear generating facility known as Wolf Creek — owned by Westar Energy Inc., Great Plains Energy Inc. and Kansas Electric Power Cooperative Inc. — on a lake shore near Burlington, Kansas.
The possibility of a Russia connection is particularly worrisome, former and current officials say, because Russian hackers have previously taken down parts of the electrical grid in Ukraine and appear to be testing increasingly advanced tools to disrupt power supplies. [Continue reading…]
Bush administration official blasts Trump over Russia
Reuters reports: A former U.S. diplomat who served under Republican President George W. Bush criticized the Trump administration on Wednesday for failing to do more to investigate allegations that Russia sought to meddle in the 2016 U.S. election.
“Russia’s going to do this again,” Nicholas Burns, who was undersecretary of state from 2005 to 2008, testified to the Senate Intelligence Committee.
“Russia’s our most dangerous adversary in the world today, and if he continues to refuse to act, it’s a dereliction of the basic duty to defend the country,” Burns said. [Continue reading…]
Europe has been working to expose Russian meddling for years
The Washington Post reports: As the United States grapples with the implications of Kremlin interference in American politics, European countries are deploying a variety of bold tactics and tools to expose Russian attempts to sway voters and weaken European unity.
Across the continent, counterintelligence officials, legislators, researchers and journalists have devoted years — in some cases, decades — to the development of ways to counter Russian disinformation, hacking and trolling. And they are putting them to use as never before.
Four dozen officials and researchers interviewed recently sounded uniformly more confident about the results of their efforts to counter Russian influence than officials grappling with it in the United States, which one European cyber-official described as “like watching ‘House of Cards.’ ”
“The response here has been very practical,” observed a senior U.S. intelligence official stationed in Europe. “Everybody’s looking at it.”
In the recent French elections, the Kremlin-friendly presidential candidate lost to newcomer Emmanuel Macron, who was subjected to Russian hacking and false allegations in Russian-sponsored news outlets during the campaign. In Germany, all political parties have agreed not to employ automated bots in their social media campaigns because such hard-to-detect cybertools are frequently used by Russia to circulate bogus news accounts. [Continue reading…]
Evidence is mounting that Russia took four clear paths to meddle in the U.S. election
Business Insider reports: It was September 2015 when the FBI first noticed that Russian hackers had infiltrated a computer system belonging to the Democratic National Committee.
It was the first sign that Moscow was attempting to meddle in the presidential election.
Nearly a year later, further reporting and testimony from current and former intelligence officials have painted a portrait of Russia’s election interference as a multifaceted, well-planned, and coordinated campaign aimed at undermining the backbone of American democracy: free and fair elections.
Now, as FBI special counsel Robert Mueller and congressional intelligence committees continue to investigate Russia’s election interference, evidence is emerging that the hacking and disinformation campaign waged at the direction of Russian President Vladimir Putin took at least four separate but related paths.
The first involved establishing personal contact with Americans perceived as sympathetic to Moscow — such as former Defense Intelligence Agency chief Michael Flynn, former Trump campaign chairman Paul Manafort, and early Trump foreign-policy adviser Carter Page — and using them as a means to further Russia’s foreign-policy goals.
The second involved hacking the Democratic National Committee email servers and then giving the material to WikiLeaks, which leaked the emails in batches throughout the second half of 2016.
The third was to amplify the propaganda value of the leaked emails with a disinformation campaign waged predominantly on Facebook and Twitter, in an effort to use automated bots to spread fake news and pro-Trump agitprop.
And the fourth was to breach US voting systems in as many as 39 states leading up to the election, in an effort to steal registration data that officials say could be used to target and manipulate voters in future elections. [Continue reading…]
How an entire nation became Russia’s test lab for cyberwar
Wired reports: The clocks read zero when the lights went out.
It was a Saturday night last December, and Oleksii Yasinsky was sitting on the couch with his wife and teenage son in the living room of their Kiev apartment. The 40-year-old Ukrainian cybersecurity researcher and his family were an hour into Oliver Stone’s film Snowden when their building abruptly lost power.
“The hackers don’t want us to finish the movie,” Yasinsky’s wife joked. She was referring to an event that had occurred a year earlier, a cyberattack that had cut electricity to nearly a quarter-million Ukrainians two days before Christmas in 2015. Yasinsky, a chief forensic analyst at a Kiev digital security firm, didn’t laugh. He looked over at a portable clock on his desk: The time was 00:00. Precisely midnight.
Yasinsky’s television was plugged into a surge protector with a battery backup, so only the flicker of images onscreen lit the room now. The power strip started beeping plaintively. Yasinsky got up and switched it off to save its charge, leaving the room suddenly silent.
He went to the kitchen, pulled out a handful of candles and lit them. Then he stepped to the kitchen window. The thin, sandy-blond engineer looked out on a view of the city as he’d never seen it before: The entire skyline around his apartment building was dark. Only the gray glow of distant lights reflected off the clouded sky, outlining blackened hulks of modern condos and Soviet high-rises.
Noting the precise time and the date, almost exactly a year since the December 2015 grid attack, Yasinsky felt sure that this was no normal blackout. He thought of the cold outside—close to zero degrees Fahrenheit—the slowly sinking temperatures in thousands of homes, and the countdown until dead water pumps led to frozen pipes.
That’s when another paranoid thought began to work its way through his mind: For the past 14 months, Yasinsky had found himself at the center of an enveloping crisis. A growing roster of Ukrainian companies and government agencies had come to him to analyze a plague of cyberattacks that were hitting them in rapid, remorseless succession. A single group of hackers seemed to be behind all of it. Now he couldn’t suppress the sense that those same phantoms, whose fingerprints he had traced for more than a year, had reached back, out through the internet’s ether, into his home.
The Cyber-Cassandras said this would happen. For decades they warned that hackers would soon make the leap beyond purely digital mayhem and start to cause real, physical damage to the world. In 2009, when the NSA’s Stuxnet malware silently accelerated a few hundred Iranian nuclear centrifuges until they destroyed themselves, it seemed to offer a preview of this new era. “This has a whiff of August 1945,” Michael Hayden, former director of the NSA and the CIA, said in a speech. “Somebody just used a new weapon, and this weapon will not be put back in the box.”
Now, in Ukraine, the quintessential cyberwar scenario has come to life. Twice. On separate occasions, invisible saboteurs have turned off the electricity to hundreds of thousands of people. Each blackout lasted a matter of hours, only as long as it took for scrambling engineers to manually switch the power on again. But as proofs of concept, the attacks set a new precedent: In Russia’s shadow, the decades-old nightmare of hackers stopping the gears of modern society has become a reality. [Continue reading…]
The scope of the Russian threat
The New York Times reports: Lost in the showdown between President Trump and James B. Comey that played out this past week was a chilling threat to the United States. Mr. Comey, the former director of the F.B.I., testified that the Russians had not only intervened in last year’s election, but would try to do it again.
“It’s not a Republican thing or Democratic thing — it really is an American thing,” Mr. Comey told the Senate Intelligence Committee. “They’re going to come for whatever party they choose to try and work on behalf of. And they’re not devoted to either, in my experience. They’re just about their own advantage. And they will be back.”
What started out as a counterintelligence investigation to guard the United States against a hostile foreign power has morphed into a political scandal about what Mr. Trump did, what he said and what he meant by it. Lawmakers have focused mainly on the gripping conflict between the president and the F.B.I. director he fired with cascading requests for documents, recordings and hearings.
But from the headquarters of the National Security Agency to state capitals that have discovered that the Russians were inside their voter-registration systems, the worry is that attention will be diverted from figuring out how Russia disrupted American democracy last year and how to prevent it from happening again. Russian hackers did not just breach Democratic email accounts; according to Mr. Comey, they orchestrated a “massive effort” targeting hundreds of — and possibly more than 1,000 — American government and private organizations since 2015.
“It’s important for us in the West to understand that we’re facing an adversary who wishes for his own reasons to do us harm,” said Daniel Fried, a career diplomat who oversaw sanctions imposed on Russia before retiring this year. “Whatever the domestic politics of this, Comey was spot-on right that Russia is coming after us, but not just the U.S., but the free world in general. And we need to take this seriously.” [Continue reading…]
Inside Russia’s social media cyberwar on America
Time reports: On March 2, a disturbing report hit the desks of U.S. counterintelligence officials in Washington. For months, American spy hunters had scrambled to uncover details of Russia’s influence operation against the 2016 presidential election. In offices in both D.C. and suburban Virginia, they had created massive wall charts to track the different players in Russia’s multipronged scheme. But the report in early March was something new.
It described how Russia had already moved on from the rudimentary email hacks against politicians it had used in 2016. Now the Russians were running a more sophisticated hack on Twitter. The report said the Russians had sent expertly tailored messages carrying malware to more than 10,000 Twitter users in the Defense Department. Depending on the interests of the targets, the messages offered links to stories on recent sporting events or the Oscars, which had taken place the previous weekend. When clicked, the links took users to a Russian-controlled server that downloaded a program allowing Moscow’s hackers to take control of the victim’s phone or computer–and Twitter account.
As they scrambled to contain the damage from the hack and regain control of any compromised devices, the spy hunters realized they faced a new kind of threat. In 2016, Russia had used thousands of covert human agents and robot computer programs to spread disinformation referencing the stolen campaign emails of Hillary Clinton, amplifying their effect. Now counterintelligence officials wondered: What chaos could Moscow unleash with thousands of Twitter handles that spoke in real time with the authority of the armed forces of the United States? At any given moment, perhaps during a natural disaster or a terrorist attack, Pentagon Twitter accounts might send out false information. As each tweet corroborated another, and covert Russian agents amplified the messages even further afield, the result could be panic and confusion.
For many Americans, Russian hacking remains a story about the 2016 election. But there is another story taking shape. Marrying a hundred years of expertise in influence operations to the new world of social media, Russia may finally have gained the ability it long sought but never fully achieved in the Cold War: to alter the course of events in the U.S. by manipulating public opinion. The vast openness and anonymity of social media has cleared a dangerous new route for antidemocratic forces. “Using these technologies, it is possible to undermine democratic government, and it’s becoming easier every day,” says Rand Waltzman of the Rand Corp., who ran a major Pentagon research program to understand the propaganda threats posed by social media technology. [Continue reading…]
North Korea said to be target of inquiry over $81 million cyberheist
The New York Times reports: Federal prosecutors are investigating North Korea’s possible role in the theft of $81 million from the central bank of Bangladesh in what security officials fear could be a new front in cyberwarfare.
The United States attorney’s office in Los Angeles has been examining the extent to which the North Korea government aided and abetted the bold heist in February 2016, according to a person briefed on the investigation who was not authorized to speak publicly.
In the theft, the attackers, using a global payment messaging system known as Swift, were able to persuade the Federal Reserve Bank of New York to move money from the Bangladesh bank to accounts in the Philippines. The Swift system is used by some 11,000 banks and companies to transfer money from one country to another.
In the months that followed the Bangladesh heist, it was disclosed that cyberthieves had also attacked banks in Vietnam and Ecuador using Swift. [Continue reading…]
Why Wikileaks? Why now?
Am genuinely curious why group who hacked CIA laundering via Wikileaks, rather than a new cutout. Seems likely to undermine their message.
— Pwn All The Things (@pwnallthethings) March 7, 2017
Fred Kaplan writes: Tuesday’s WikiLeaks release exposing thousands of detailed documents on CIA hacking tools is an unbridled attack on U.S. intelligence operations with little or no public benefit. It makes no claim or pretense that the CIA has used these tools to engage in domestic surveillance or any other illegal activity. Most whistleblowers who leak national security secrets take care to avoid revealing where the secrets come from — the “sources and methods” of the intelligence. These documents are about nothing but sources and methods. [Continue reading…]
Reuters reports: A longtime intelligence contractor with expertise in U.S. hacking tools told Reuters the documents included correct “cover” terms describing active cyber programs.
“People on both sides of the river are furious,” he said, referring to the CIA and the eavesdropping National Security Agency based in Fort Meade, Maryland. “This is not a Snowden-type situation. This was taken over a long term and handed over to WikiLeaks.” [Continue reading…]
In a press release, Wikileaks said: Recently, the CIA lost control of the majority of its hacking arsenal including malware, viruses, trojans, weaponized “zero day” exploits, malware remote control systems and associated documentation. This extraordinary collection, which amounts to more than several hundred million lines of code, gives its possessor the entire hacking capacity of the CIA. The archive appears to have been circulated among former U.S. government hackers and contractors in an unauthorized manner, one of whom has provided WikiLeaks with portions of the archive.
In a statement to WikiLeaks the source details policy questions that they say urgently need to be debated in public, including whether the CIA’s hacking capabilities exceed its mandated powers and the problem of public oversight of the agency. The source wishes to initiate a public debate about the security, creation, use, proliferation and democratic control of cyberweapons.
Names, email addresses and external IP addresses have been redacted in the released pages (70,875 redactions in total) until further analysis is complete. [Continue reading…]
The Atlantic reports: WikiLeaks appears to be shifting its strategy with its latest document dump. In the past, it has let the public loose on its leaked documents with little more than a few paragraphs of introduction, occasionally building search functions to let users sift through the largest dumps. The CIA leak, on the other hand, came with a detailed press release and analysis of the some key findings from the documents, written in a journalistic style.
Uncharacteristically, WikiLeaks appears to have gone out of its way to redact sensitive information and withhold malicious code from the CIA documents it made public. That’s a slight departure from previous leaks, which were wholly unfiltered. [Continue reading…]
Given that it has become increasingly difficult to differentiate between Wikileaks the organization and Julian Assange the individual, I have my doubts that the massive number of redactions and carefully crafted press release should necessarily be attributed to a shift in strategy on the part of Wikileaks/Assange. This may in fact be the way the leaks were delivered: pre-packaged.
In other words, the leaker(s) were just as concerned about how this information got out as they were with its contents — and that begs the question (as posed by @pwnallthethings): why use Wikileaks?
If, as the source is alleged to claim, the goal here is to generate public debate, why use such a flawed messenger — a messenger widely viewed as operating in the service of the Russian intelligence.
The source’s choice of going through Wikileaks suggests they were opting for a suitably malleable conduit and wanted to reach a target audience that thinks little or cares less about Julian Assange’s agenda.
Journalists are hamstrung (or to put it less kindly, incredibly easy to manipulate) in this situation. The key questions are about the source of leaks and the agenda being pursued, yet these are at this time matters of pure conjecture. The alternative to speculation is to focus on the content and get distracted by smart TV vulnerabilities etc.
Yet the source/Wikileaks is in large part teeing this up for political debate and casting the CIA as a rogue intelligence agency — a narrative that surely plays well inside the White House.
As is often the case, Donald Trump’s current silence is much more telling than his tweets.
