Ben D, a commenter at this site and Arms Control Wonk is skeptical about my assertion that Siemens SCADA software is being used at Iran’s Bushehr nuclear facility. I based that claim on a UPI photograph that led the German industrial security expert, Ralph Langner, to speculate that Bushehr was the intended target of the Stuxnet malware.
These are Ben’s qualms:
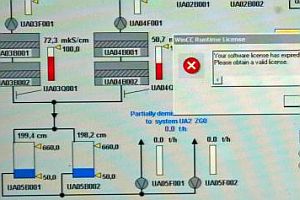
Concerning the UPI image of a control panel with a MS look window superimposed that says.. “WinCC Runtime License: Your software license has expired. Please obtain a valid license”, well it doesn’t prove a thing.
First of all, the WinCC window could so easily be a photo- shopped overlay on the image of a process control panel.
Secondly, the Control Panel image is typical of process control panels everywhere and even if the WinCC window was not photo-shopped, what has that got to do with Bushehr. There is nothing else in the image to provide any information whatsoever about the local environment to provide any context as to its locality or purpose.
Thirdly, UPI does not provide a source for anyone claiming that the UPI Photo by Mohammad Kheirkhah is actually Bushehr, they just provide a narrative to imply that it is.
Fourthly, Ralph Lagner is not claiming the UPI image is actually genuine or that it is of Bushehr, he merely prefaces his speculative theory with ” If the picture is authentic, which I have no means of verifying,….”.
Has the image been doctored? I’m not in a position to determine that, but the Hacker Factor Blog did some image analysis and concluded that it was not doctored. He has other reasons for questioning whether it was taken at Bushehr but found no evidence that it had been manipulated with Photoshop.
 This image apparently confirms that the photograph is of a computer monitor and the continuity in the ripple pattern across the part of the screen where the WinCC message appears seems to confirm that this was not inserted from a different screen image. (This ripple pattern can be seen both in the blue image and the close-up image.)
This image apparently confirms that the photograph is of a computer monitor and the continuity in the ripple pattern across the part of the screen where the WinCC message appears seems to confirm that this was not inserted from a different screen image. (This ripple pattern can be seen both in the blue image and the close-up image.)
So, assuming that the WinCC expired-licence message was actually appearing on that monitor screen, is there any evidence that the monitor and the control system it depicts is in Bushehr?
 Frankly, I was willing to accept that UPI was not misrepresenting or incorrectly labeling its photos, but still, some additional analysis was both in order and turned out to be fruitful. There is indeed evidence that this image depicts a Bushehr control system.
Frankly, I was willing to accept that UPI was not misrepresenting or incorrectly labeling its photos, but still, some additional analysis was both in order and turned out to be fruitful. There is indeed evidence that this image depicts a Bushehr control system.
The elements in the schematic have a uniform numbering system — UA04B001, UA04B002 etc.
 Another UPI photograph appears to show the physical components depicted on the system control monitor. This vessel shown on the right is numbered UA06B002. That particular number doesn’t appear on the monitor image but it’s hard to believe that this is not part of the same system.
Another UPI photograph appears to show the physical components depicted on the system control monitor. This vessel shown on the right is numbered UA06B002. That particular number doesn’t appear on the monitor image but it’s hard to believe that this is not part of the same system.
OK. But maybe the screen image and the image of an Iranian technician turning a valve were taken some place other than Bushehr.
 Well, UPI’s photographer was one among a group of international journalists who were shown around Bushehr in February 2009. They included Jon Leyne, a reporter for the BBC, and a video in his report shows the same assembly of pale gray vessels that appear in the UPI photo. Indeed, an AFP image in the same report shows the same technician, from a different angle, doing his valve-turning performance for the assembled press.
Well, UPI’s photographer was one among a group of international journalists who were shown around Bushehr in February 2009. They included Jon Leyne, a reporter for the BBC, and a video in his report shows the same assembly of pale gray vessels that appear in the UPI photo. Indeed, an AFP image in the same report shows the same technician, from a different angle, doing his valve-turning performance for the assembled press.
With the evidence that I’ve laid out I will assert with even more confidence that the Bushehr nuclear plant uses Siemens WinCC SCADA software. I also see little reason to doubt that Iranian officials were telling the truth when they said that Stuxnet had been found on personal computers used by the facility’s operators. What I remain skeptical about is their claim that the malware did not penetrate the system. How confident the Iranians are on that question may become evident in the coming months when the plant begins or fails to begin generating electricity.


Thank you Paul for an informative post, however overall it doesn’t strengthen your case but weakens it.
The post by Dr. Neal Krawetz ( Image Analysis, Mass Media, Forensics) on The Hacker Factor Blog you linked to writes that he has problems with that UPI photo, not that it is doctored, but that it has been misrepresented as being from Bushehr/Iran. This is also what my third point was raising.
http://www.hackerfactor.com/blog/index.php?/archives/396-No-Nukes.html
[quote]Frankly, I see a bunch of problems with this picture. It really looks fake to me.
I have trouble believing that a real photo from within an Iranian nuclear plant would be using unregistered/unlicensed code. It makes for a great joke, but it doesn’t seem practical. I mean, seriously, Iran paid Russia $800 million for the facility, and you think it would include unregistered software?[/quote]
The Hacker Factor Blog’s overall opinion is that while the UPI photo does not provide any clue as to the plant in which it was taken, it does provide a clue as to what the industrial plant was processing,…crap 🙂
Concerning the text on the monitor screen…
[quote]
Image Text
Since I can read the text, I can’t help but notice that it has a section for “Sulfuric Acid Storage and Feeding” (center, right) and “Lime Milk Preparation and Dosing” (bottom, center).
Sulfuric Acid isn’t startling. It is used in most power plants and water treatment facilities. However, Lime Milk is primarily used in water and sewage treatment plants and not power plants.
Another section discusses “Polyacryl Preparation and Dosing” (bottom, right). Polyacrylamide is primarily used in wastewater treatment. (“Wastewater” as in toilets and street drains.)
Moreover, the bottom left has a section on “Waste Water neutralization”. This really looks like a schematic for a sewage treatment facility and not a nuclear power plant.[/quote]
The claim that the UPI photo is of Bushehr is not supported by an expert in forensics and image analysis.
[quote]Journalistic Excellence
UPI has the tagline “Journalistic Excellence”. However, I think they failed to research this picture. Is it even showing a nuclear power plant’s schematic? How does UPI know that this image is legitimate? If someone were to get a camera in there, I would think that more incriminating photos would come out besides an error message on a screen…
Iran is known to release doctored images of old photos and rewrite history. However, this picture does not appear to be doctored. It just looks misrepresented.
Don’t get me wrong, I get the joke — an error message about unregistered software at a nuclear power plant. Funny. But I think the real joke is that UPI ran with it.
Posted by Dr. Neal Krawetz in Image Analysis, Mass Media, Forensics[/quote]
Ben – It’s not evident to me that you actually read my post or examined the evidence. Please explain why the same numbering system is being used in the schematic and on the physical vessels which are definitely located in Bushehr. I say definitely located there because they were photographed and reported by UPI, AFP and the BBC at the same time – February 2009.
Neal Krawetz bases a significant part of his argument on the fact that the close-up shot of the monitor was taken with a camera with some dust on the lens and the other photos taken inside Bushehr were taken with a clean lens. Has he never seen a press photographer carrying more than one camera?
Thankfully, the photographer whose work is being analysed has provided his own explanation about this discrepancy: “I was using two cameras that day, one for my photo tele lens and one for the wide one.” (That’s from a comment by Mohammad Kheirkhah.)
And one more point – just so that we can be clear that Neal Krawetz is not an authoritative source on the operation of nuclear power plants. He blithely asserts: “Lime Milk is primarily used in water and sewage treatment plants and not power plants.”
According to Siemens, lime milk is used for “water treatment” in “nuclear power stations”. Don’t take my word for it. Read about it here: http://www.wallace-tiernan.de/WT/technische_pdf/WT.330.106.000.IE.PS.0607.A-758-G.pdf
Oh and Paul, I would also like to address this…….
“What I remain skeptical about is their claim that the malware did not penetrate the system. How confident the Iranians are on that question may become evident in the coming months when the plant begins or fails to begin generating electricity.”
There are already rumours that there is a delay, whether true or false will be revealed in time, but I wouldn’t write too much into it with respect to the Stuxnet virus as being responsible.
Russia is the prime contractor for Bushehr and so far as I’m aware they will still be responsible until it is shown to be operational. If there is a problem then the Russians would be the first to know and it would already be known as we speak. You and I are not privy to any leaks directly about the status of ongoing acceptance testing but if there has been a leak to the effect that there is a problem and those PTB waging psyop warfare against Iran got to know (intelligence after all is their job), then it would be ‘standard operational procedure’ to take advantage and ‘spin’ it in a way that shows Iran to be vulnerable and weak, rather than allow due process to reveal mundane technical reasons that would most likely be really behind it.
Like in any chess game, the one that is able to see ahead the more moves has the advantage….
Paul, I did read your post but I was impressed with the explanation of Neal Krawetz that the control schematic was not of a power station but of a sewerage treatment plant. This is consistent with what the Siemens spokesperson explained about that Windows is not to operate critical processes in plants, so it can be inferred that the UPI photo is from a non-critical plant process somewhere, location yet unknown.
For that reason, while the pictures you posted concerning the numbering on the control schematic and equipment are consistent, this does nothing towards proving they come from the Bushehr nuclear plant, but are more consistent with a water/sewerage plant. Now it’s true I’m no industrial chemist to verify the assessment of Neal Krawetz, but unless he can be shown to be misinforming his readers, I’m accepting his explantion on what sort of process the control schematic is involved in.
Concerning the photographer Mohammad Kheirkhah, Photographer from Bay Area, USA, and who does work for the BBC, I find this coincidence remarkable. 🙂
[quote]Hi, I am the photographer of this picture and just found this post accidentally. I took this picture in Bushehr Power Plant.[/quote]
If you have got my drift by now, you know that I suspect there is some ‘funny’ business going on surrounding this story of Stuxnet and Bushehr, and this sort of ‘accident’ just adds to the credibility of it being a non-contrived reality.
But how do we know for certain that the “man” pictured in the photos allegedly taken at the Bushehr nuclear facility in Iran here on Earth, is not actually an android (who may, or may not, dream of electric sheep) in a facility on Mars? Answer me that!
And what about the Heisenberg Uncertainty Principle as interpreted, or not, by the Coen brothers? “Enquiring minds want to know.”
P.S. This country (if not humanity in general) desperately needs Philip K. Dick’s ’empathy machine’. And not just for androids (in the event G-d should ever bless or curse us with them)!
P.S.S. And does anyone beside(s) me think it’s “mighty peculiar” that the name of Iran’s first nuclear power plant contains prominently within it the Bush family name (as the family, whilst in England, anglicized it from their uncomfortably Germanic-sounding original name)? [lol, or not]
Ben D October 4, 2010 at 12:20 am
Paul, I did read your post but I was impressed with the explanation of Neal Krawetz.
>>>>>>>>>>>>
You just aren’t convinving Ben….. using Krawetz as an authority is highly suspect.
I have seen Krawetz’s credentials and an imaging expert he is definitely not.
Further he is considered something of a attention seeking publicity hound by more serious experts in the field……as evidenced by the Obama hullaboo he started.
“Dr. Neal Krawetz says new Certificate of Live Birth, claiming Obama was born in Hawaii, is another forgery By JesseParsons1983 Fort Collins : CO : USA | 11 months ago
Sentinel Radio reports with Dr. Krawetz’s reply to an email describing the document: “This [Certificate of Live Birth] is the single worst forgery that I have ever seen. It is as if…”
Actually Renfro, I had never heard of Neal Krawetz before, I just followed Paul’s link to his post so I naturally took it as a given that if Paul accepted his expertise to support his argument that the photo was not doctored, then the rest of his analysis was also to considered reasonable. In fact I do think he made some convincing arguments, though I will, when time permits, look further into the question of his reputation which you raised.
Yeh dickerson, thanks for the reminder not to get carried away,…. c’mon folks, move along, there’s nothing to see here!!!
Ben D October 4, 2010 at 5:24 am
Yea, these days you always have to consider the source.